If you’ve been on social media recently, you’ve probably seen your friends (and celebrities) finding their fine art doppelgangers via the Google Arts and Culture app – and maybe you’ve felt left out of the fun. That’s because Illinois is one of only two states with laws regulating the use of biometrics, like your face or your fingerprint, to authenticate your identity.
Biometric methods are quickly becoming the authentication method of choice for smartphone manufacturers, financial institutions and even U.S. border patrol. And while it can be a lot of fun to animate an emoji to match your face, the long-term implications of using biometric data are still uncharted.
Justin O’Neill Kay, a partner with the Chicago firm Drinker Biddle & Reath, joins us to talk about how biometrics can unlock more than your phone.
We asked Kay several key questions via email about Illinois’ laws on biometric data. Below, our Q&A.
![]()
Can you explain Illinois’ biometrics legislation, particularly as it compares with other states?
Illinois’ biometric legislation is known as the Biometric Information Privacy Act, referred to as “BIPA” for short. BIPA became law in October 2008, and was the first law of its kind in the United States. Many other states have considered or are currently considering their own biometric legislation, but right now, there are only two other states with laws like BIPA: Texas and Washington. Texas’s version became law in 2009, and Washington’s version became law in 2017.
BIPA was passed to address concerns about the collection of biometrics following the collapse of a company called Pay By Touch. Pay By Touch permitted consumers to link various accounts to their fingerprints, and then access those accounts or make a payment with a touch of their finger rather than using cash or swiping a card. When Pay By Touch went out of business in early 2008, legislators started to ask questions about what would happen with the biometrics Pay By Touch had collected. Illinois passed BIPA in response.
BIPA regulates the collection, storage, use, and destruction of “biometric identifiers” and “biometric information,” referred to together here as “biometric data.” “Biometric identifiers” specifically include “a retina or iris scan, fingerprint, voiceprint, or scan of hand or face geometry,” but specifically excludes other information, such as measurements that might be taken during a medical exam. “Biometric information” is data that is based on biometric identifiers.
As discussed in more detail below, BIPA requires individuals, corporations, and organizations that collect biometric data for any purpose to obtain a person’s written agreement before doing so. There are limited exceptions for certain groups, such as financial institutions, government, and law enforcement. BIPA also requires disclosures to be provided explaining why and how long the data will be used, requires the data to be secured, and requires the data to be destroyed after a specific period of time. BIPA also bars the sharing of the data with others except in very narrow circumstances, and bars (without exception) the sale or profiting from the data. Finally, BIPA permits individuals to sue in court for violations of BIPA in certain circumstances.
The Texas law is similar to BIPA and uses some of the same definitions, but it is a little less restrictive. For example, while BIPA applies to the collection of biometric data for any purpose (including a security purpose), the Texas law applies only to biometric identifiers that are collected for a “commercial purpose.” Also, the Texas law does not permit a person to file a lawsuit—it can be enforced only by the government.
The Washington law is significantly less restrictive than BIPA, and appears designed to correct some of the concerns businesses expressed about BIPA. Like the Texas law, the Washington law applies only when an identifier is collected for a “commercial purpose,” but only if the identifier is also added to a database. Also, the Washington law specifically excludes certain types of information included under BIPA, and does not apply when the identifier is collected for a security purpose. Like the Texas law, the Washington law can be enforced only by the government.
What are some ways the data is stored and secured? How is permission for the data typically obtained?
BIPA requires any person, company, or organization in possession of biometric data to store, transmit, and protect that data using “the reasonable standard of care” used in that person’s industry. BIPA also requires the data to be stored, protected, and transmitted using methods that are the same as or more protective than the methods used to protect other confidential and sensitive information, such as passwords, account numbers, and social security numbers.
As a practical matter, the exact ways the data is stored and secured will vary, but best practices should include encryption and access restrictions. We know from court filings, for example, that Facebook’s facial recognition process takes place on computer servers outside Illinois, and that is one of the reasons Facebook has argued that it is not required to comply with BIPA.
With regard to permissions, BIPA specifies that any person, company, or organization that obtains biometric data must first obtain a signed, written release (by clicking “I Agree,” for example). Such a release might be provided along with the standard terms and conditions that are part of interactions with many businesses, or as part of pre‐employment paperwork.
Are the consumers made aware of how and when their data might be searched?
Consumers are not necessarily alerted to how and when their data is searched, but BIPA does require that consumers be made aware of several items with regard to their data. First, a consumer’s biometric data cannot be secretly captured: BIPA requires that the person or entity collecting biometric data inform the consumer in writing that his or her data is being collected, and obtain a signed release from that person permitting the collection. Second, a consumer must be told why his or her data is being collected: BIPA requires that the person or entity collecting biometric data inform the consumer in writing of the specific purpose for the collection and length of time the data will be used. Third, a consumer must be told how long the data will be stored: BIPA requires that the person or entity in possession of biometric data provide publicly available policies and guidelines for retaining and destroying biometric data. BIPA also specifies that the data must be destroyed when the purpose for collecting the data is satisfied, or within three years of the last interaction with the consumer, whichever occurs first.
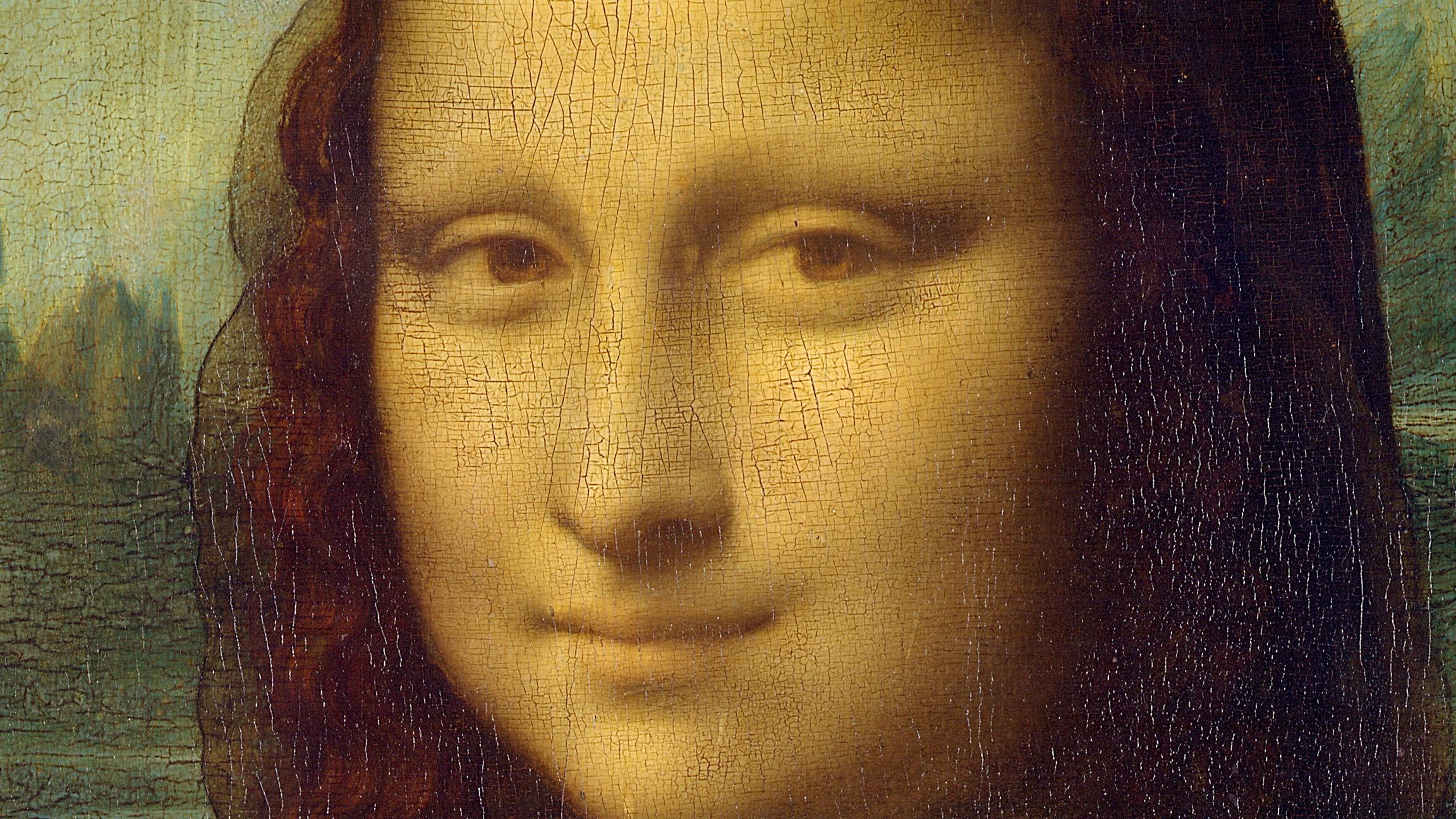 Close-up of “Mona Lisa” by Leonardo da Vinci
Close-up of “Mona Lisa” by Leonardo da Vinci
What happens if a match is false?
There are two types of match errors: false acceptance and false rejection. A false acceptance is worrisome because it permits a person to access data or a location or authorize an action (such as a payment or transfer of funds) that a person is not actually permitted to access or authorized to do. A false rejection, on the other hand, is more frustrating than worrisome because it refuses access to someone otherwise authorized. While an inconvenience, that person presumably will have back‐up options for verification: an iPhone, for example, will request a password or passcode after a certain number of failed biometric authentication attempts.
The goal for biometric authentication is to reduce to zero the percentage of false acceptances, while at the same time making the percentage of false rejections as small as possible.
Are biometrics data portable across vendors/databases?
Under BIPA, data can be shared, but only under limited circumstances: if the consumer provides his or her consent, if sharing the data completes a financial transaction authorized by the consumer, or if sharing the data is required by law or a warrant or subpoena. Absent one of those exceptions, sharing a consumer’s biometric data with another vendor would be considered a violation of BIPA.
Can businesses be trusted to use these for security and not marketing?
The Illinois legislature appears not to have trusted businesses to voluntarily limit their use of biometric data, because it specifically banned selling, leasing, trading, or otherwise profiting from a person's biometric data as part of BIPA. In addition, BIPA requires the person or entity collecting biometric data to inform the consumer in writing of the specific purpose for the collection and length of time the data will be used.
But the Illinois legislature appears to be skeptical of businesses’ use of data generally. In July 2017, the Illinois legislature sent to Governor Rauner a first‐of‐its‐kind bill restricting the use of geolocation data (tracking a person’s location through his or her mobile device). Governor Rauner, however, vetoed the legislation.
What can be done, legislatively or otherwise, to prevent scope creep from companies using biometrics data?
Carefully crafted legislation is the key to responsible use of biometric data, along with education of consumers and companies regarding the laws and benefits and drawbacks of providing or using biometric data. Consumers must understand that biometric authentication likely will not end the need for other forms of authentication, and companies need to be aware of the relevant laws. BIPA, for example, became law in October 2008, but it was not until the last few years that individuals filed lawsuits, and it was mostly the publicity from those lawsuits that educated companies about BIPA. In addition, few (if any) of the lawsuits brought under BIPA appear to be based on the improper use or disclosure of the data. Instead, many are based on individuals arguing that even though they voluntarily provided their information (such as they instructed a video game to scan their face in order to create an avatar), they are entitled to thousands of dollars because the company did not provide the correct disclosures and did not obtain the precise consent required under BIPA. But if the correct disclosures had been provided, most individuals probably would not have read them and instead simply clicked “I Agree.”
As discussed below, however, BIPA does require a person to be “aggrieved” (meaning, to have suffered some harm) before filing suit, and while courts have reached different conclusions on what that means, a recent decision from an Illinois Appellate court provides strong ammunition for the argument that consumers cannot file suit for violations such as the one described above.
If companies have been demonstrably insecure with personal data safety already, what’s to ensure biometric info can be safely kept?
There can be no guarantees with regard to the security of personal data (biometric or otherwise) so long as there is a human element involved, because the best procedures and precautions can be made useless by carelessness, betrayal, or creative persistence. This is a problem that governments, militaries, and intelligence agencies have dealt with for years—lives literally depend on the security of their data, and yet some of that data continues to be stolen by adversaries and/or leaked to the public.
Is this safer than other security methods from hacking?
No. Every security method presents its own challenges and benefits, and no single method of identity verification should be relied on to be 100 percent secure 100 percent of the time. The same is certainly true with regard to biometrics: the most common biometric identifiers (faces, eyes, ears, fingers) are not secured, but rather shown openly, and there are already reports of people defeating biometric authentication systems using different techniques to replicate the identifier.
As a result, the best practices for security rely on using multiple layers of different verification techniques, and biometrics offers a convenient way to add those additional layers.
What are the benefits to the consumer?
The key benefits for consumers are convenience and enhanced security. Convenience because, in most cases, there is nothing additional the consumer needs to have (such as a key, a fob, or a card) and there is nothing additional the consumer needs to do (such as remember a password). Enhanced security because, in all likelihood, biometric identifiers will be used as part of a multi‐layered authentication process, and a process that verifies the fingerprint, voiceprint, or typing cadence of the person providing the password or passphrase is more secure than one that does not.
Do you foresee a future when there’s no alternative method for authentication procedures?
It is very likely that in the near future, at least one form of biometric authentication will be required along with other authentication procedures. For example, a person could be required to provide both a fingerprint and a password to prove that the user of the password is, in fact, the person to whom that password belongs. Or, a person could be required to speak a passphrase into a microphone in order to prove that the person speaking their passphrase is, in fact, the person to whom that passphrase belongs. Geolocation data might also be used.
What is a consumer’s recourse if their information is compromised?
BIPA permits a person who is “aggrieved” by a violation to file a lawsuit, but there is some disagreement in the courts regarding what it means to be aggrieved. Some courts have determined that a consumer is required only to show that a person or entity violated the statute: for example, by failing to obtain consent before collecting the data. Other courts have determined that a consumer must also show that he or she suffered some actual harm as a result of the violation.
If a consumer is able to show that he or she is aggrieved, he or she may recover the greater of the actual damages or between $1,000 and $5,000 depending on the nature of the violation. A consumer may also obtain a court order (such as an injunction) requiring or prohibiting certain behavior, and his or her attorneys’ fees and costs.
Related stories:
 Bigger than Bitcoin: The Revolutionary Potential of Blockchain Technology
Bigger than Bitcoin: The Revolutionary Potential of Blockchain Technology
Jan. 16: International speaker Taylor Gerring explains how Bitcoin’s blockchain technology could revolutionize multiple industries.
 Can Apple and Facebook Make Their Products Less Addictive?
Can Apple and Facebook Make Their Products Less Addictive?
Jan. 15: After a public call for Apple to make its smartphones less habit-forming, we take a look at internet addiction in a digital age.
 Privacy in the Age of Voice-Activated Digital Assistants
Privacy in the Age of Voice-Activated Digital Assistants
Jan. 12, 2017: Amazon’s voice-activated digital assistant is a hot seller, but there are privacy issues.